Several states have been targeted in a new phishing campaign that impersonates state courts, DMVs, and toll collection agencies to trick victims into paying fraudulent fines. Recently, it hit my home state of Michigan and I received this message.
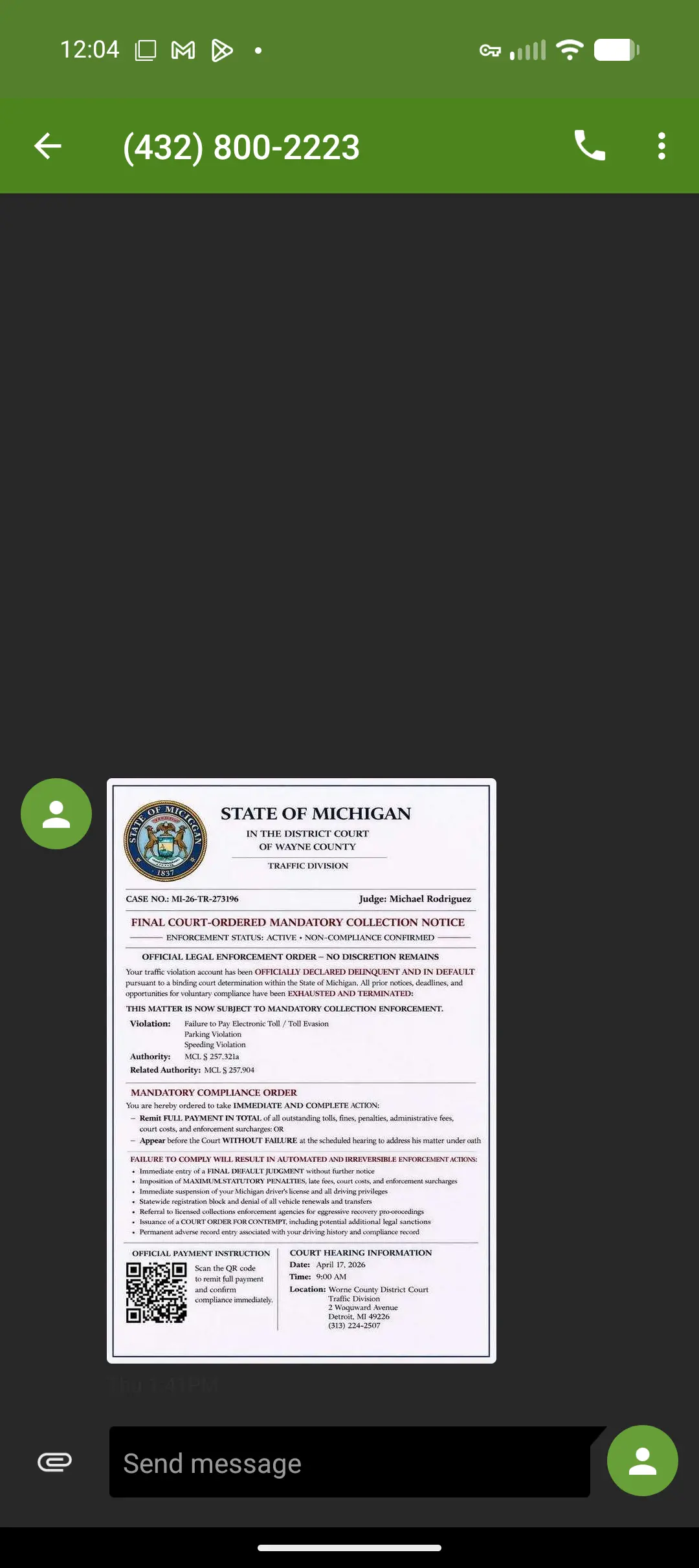
One interesting thing about this phishing campaign is that it uses images alone with no accompanying text. This is likely done to avoid any SMS filtering done by the cellular carriers. Typically, SMS filters detect spam messages using known malicious URLs, keywords, frequency of messages, and reported spam numbers. Instead of SMS (short message service), it is sent over MMS (multimedia messaging service).
While the scam relies on the impression that the message is from the State of Michigan, the area code of the phone number is (432), which is in West Texas.
Interestingly, they chose to use a QR code instead of a URL link. This is sometimes referred to as quishing. It is advantageous because the victim doesn't read the URL, they just scan it and access the website. In this case, the actual domain is "org-cmk.shop" and they added "michigan" as a subdomain.

ICANN records show the domain org-cmk.shop was registered on April 16, 2026 at 11:22 AM UTC which was the same day this phishing text was received. The domain was registered through Dynadot.
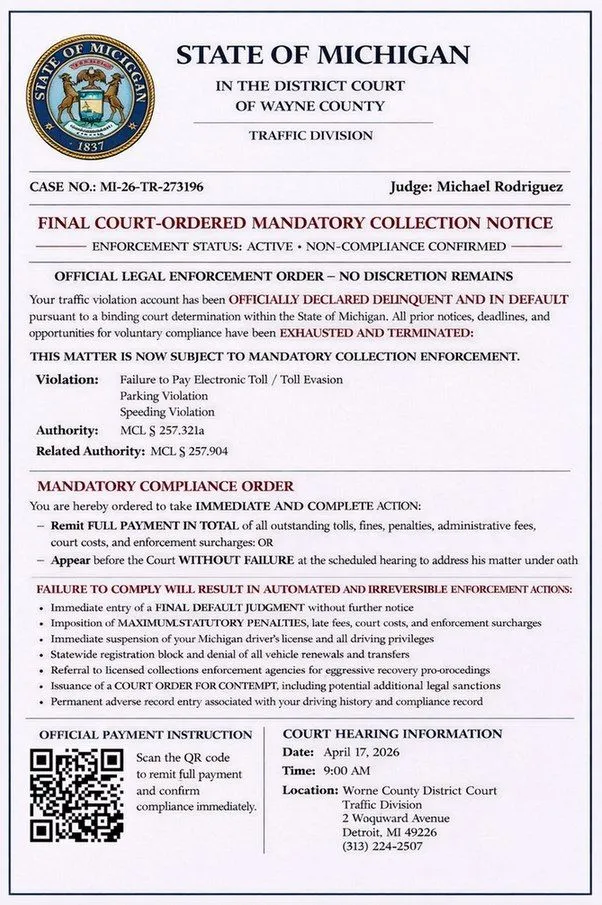
Scanning the QR code takes you to this landing page. Surprisingly, they are only requesting seven dollars for the apparent parking citation. The low amount is a deliberate strategy to lower the resistance of the victim. The real goal is to steal your payment information.
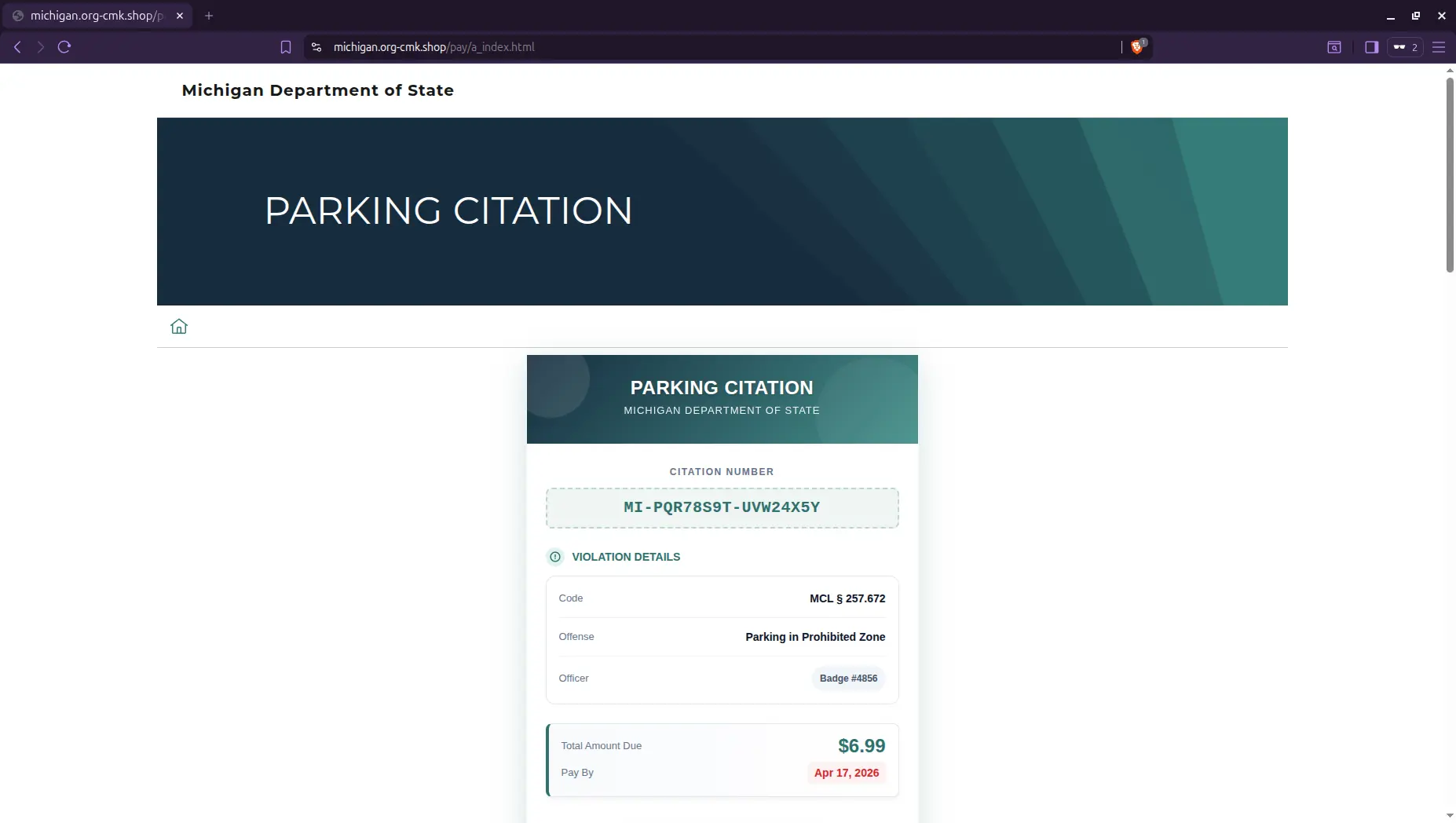
Can you spot the difference?
Phishing site
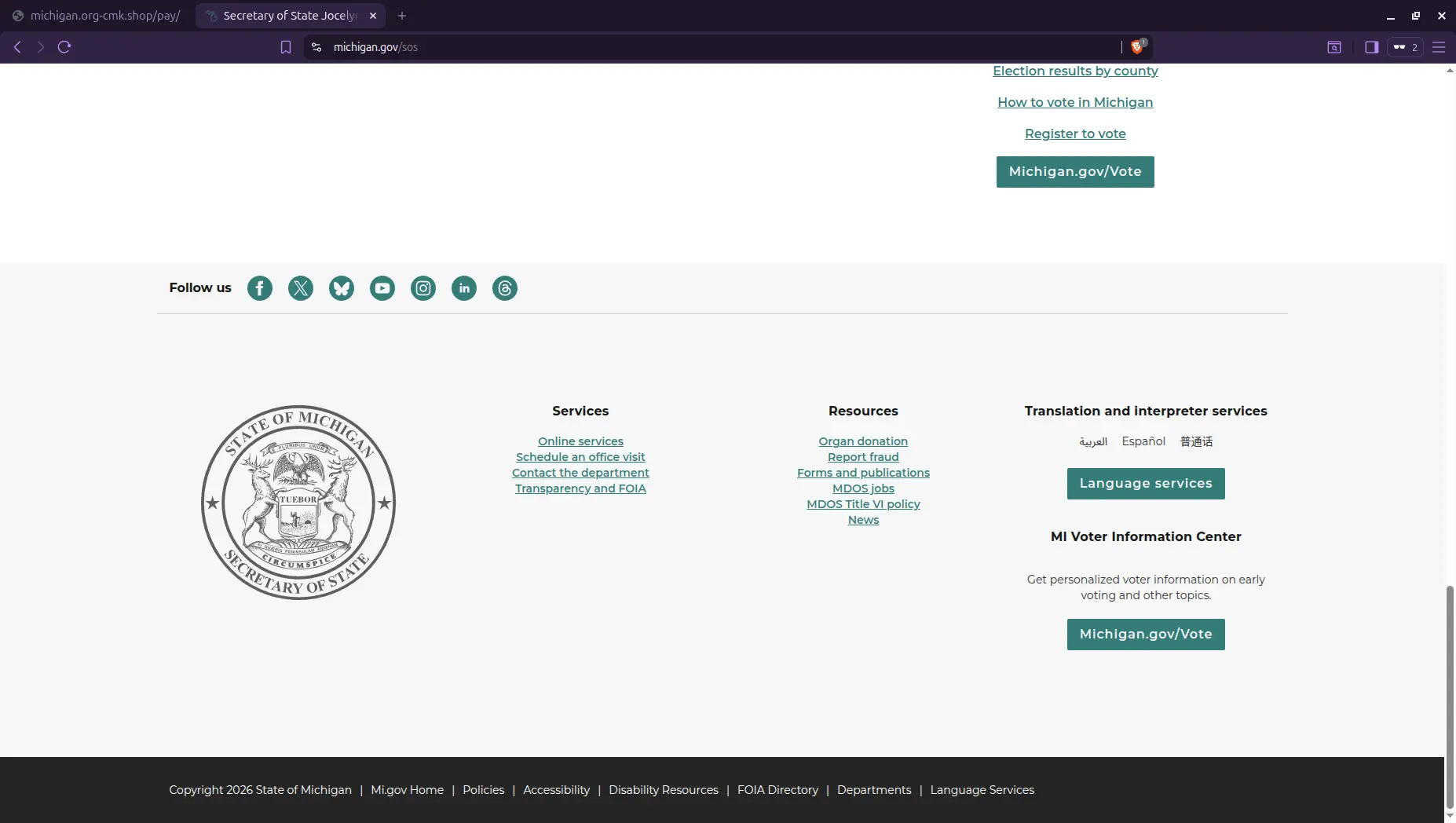
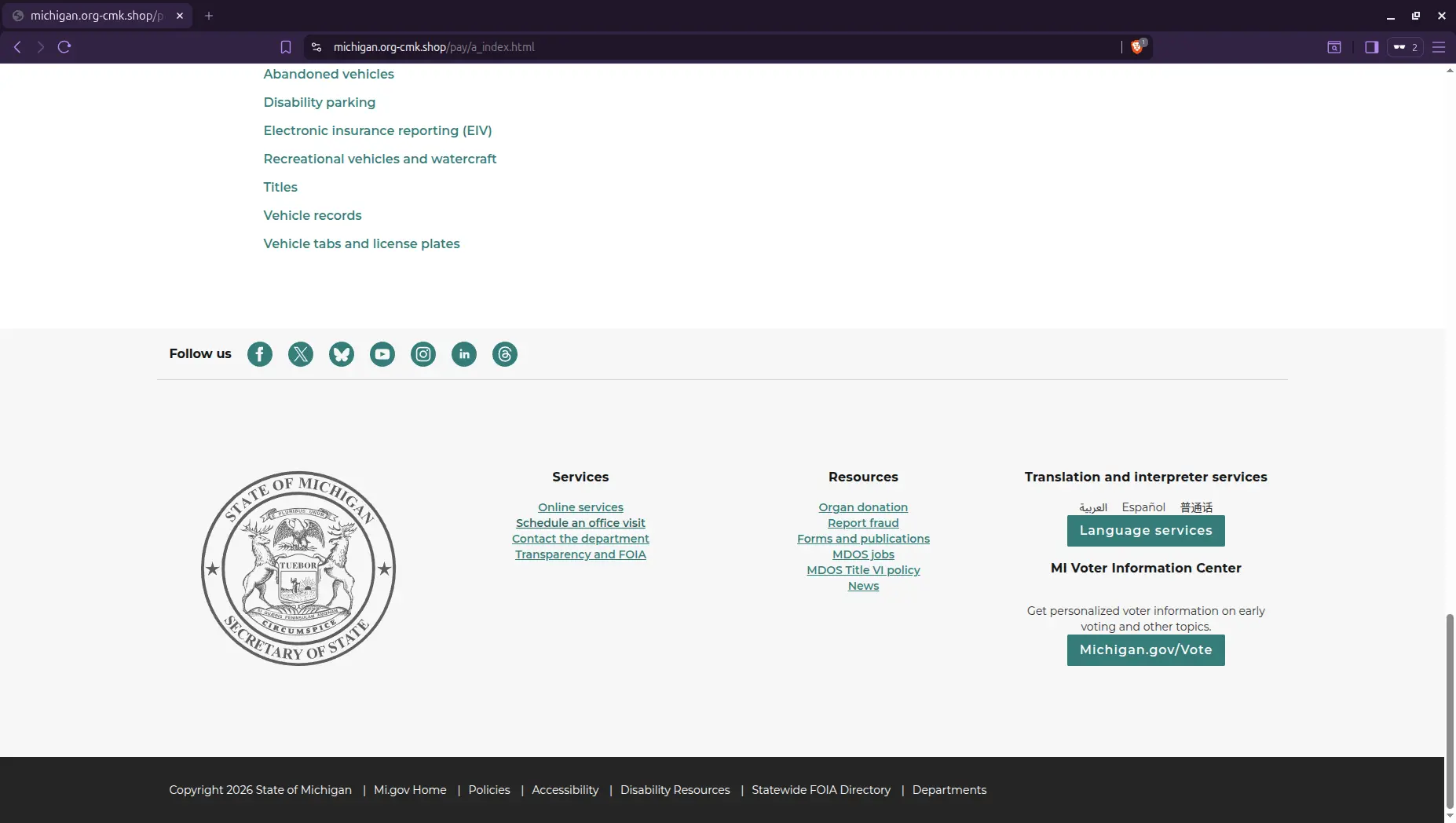
Real site
The scam site looks nearly identical to the actual michigan.gov website. If it wasn't for the malicious URL, it would be very difficult to tell them apart. The only immediate difference is that the fake site is missing the "Language Services" hyperlink in the footer.
Other Findings
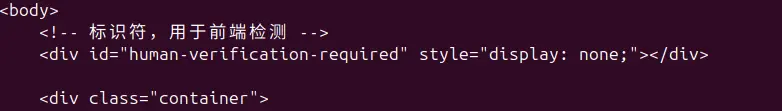
When attempting to save the home page using the 'wget' command, the server served a 403 Access Denied Page. This is interesting, suggesting they have a little more infrastructure than just a bare-bones server. Embedded in the source code for that 403 page is a comment written in Mandarin Chinese: 标识符,用于前端检测, which translates to "Identifier, used for front-end detection." This finding could be a significant clue to the origins of this phishing campaign or it could mean nothing at all.
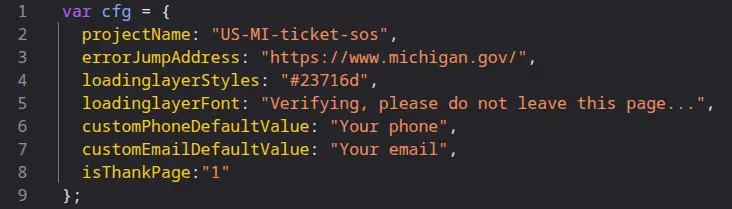
Inside common.js, two things stand out. The first is the naming convention of 'US-MI-ticket-sos'. This may suggest that state-specific campaigns exist under the same infrastructure. The second observation is they used the legitimate michigan.gov website as an error jump address. Any time a user encounters an error or navigates to an unexpected page, they get redirected to the real site.
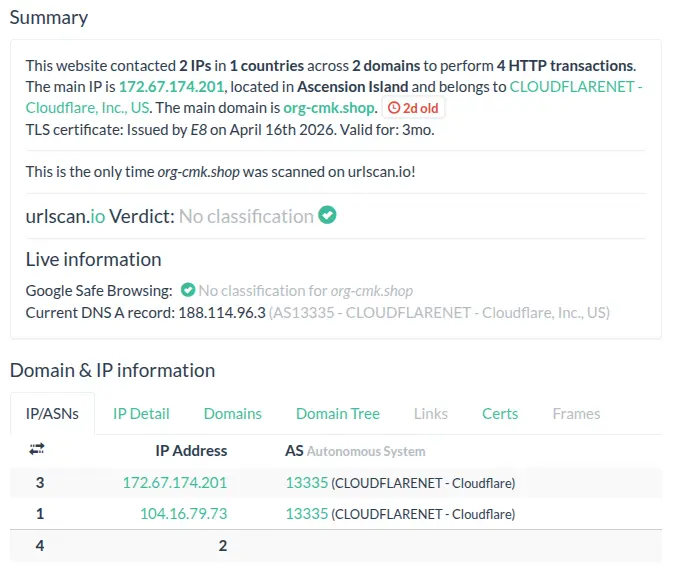
As of publishing, it's been three days since the start of this phishing campaign and the site is still up. URLScan.io reveals that Google Safe Browsing still hasn't flagged the website. Meneldor has reported the domain to Dynadot's abuse contact.
Spot and Avoid Scam Texts
The FCC has issued guidance on toll road payment scam texts. While the Michigan campaign investigated here uses more sophisticated techniques than those currently described by the FCC, their core advice remains applicable.
In essence, do not engage with the message in any way. Do not reply, click any links, or scan any QR codes. If you are genuinely concerned about an outstanding toll or court matter, verify it independently by finding the official agency's contact information yourself rather than using anything provided in the message.